Cyber Security Lifecycle – Assessments
The starting point in any organisation’s cyber security journey is to understand their systems and technologies and identify the gaps in their cyber security posture.
NeoDyne works closely with our customers to aid their understanding of their systems, through tailored assessment programs including:
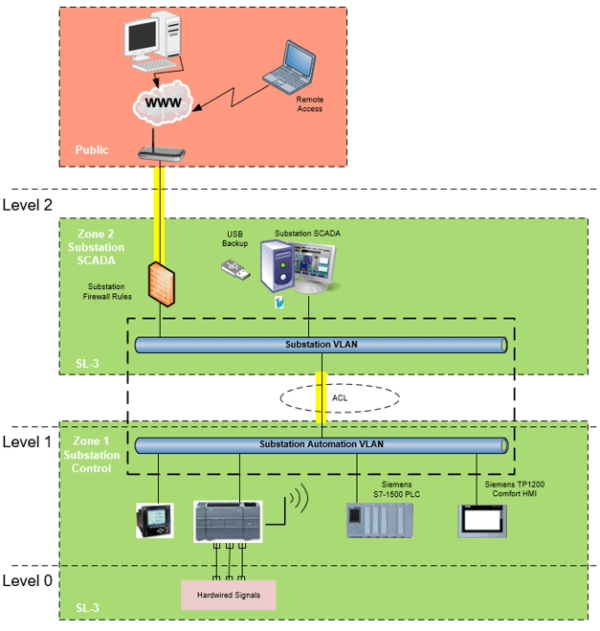
- Cyber Security Risk Assessments for new and existing OT systems
- Cyber Security Audits against the IEC-62443 standards in conjunction with our vendor partners
- Evaluation of existing Industrial OT Cyber Security policies and procedures
- Development of Reference Architectures and Zone & Conduit Diagrams
As ISA certified IEC-62443 IC33 Cyber Security Assessment Specialists, we have an in-depth understanding of the security challenges facing your organisation and have the expertise and capability to help you manage all identified potential security threats.
Driving technology for leading brands
Integration & Digital Manufacturing Customers
We supply the Life Science, Food & Beverage, Data Centre and Energy industries.
Our key markets are for robust applications requiring innovation, reliability, longevity and specialised know-how.

















Connect with a NeoDyne Engineer
Do you have a project
to discuss?
Are you facing an engineering challenge that requires expert guidance? Or a vision that needs to be brought to life? Meet our innovators, and together, we’ll shape tomorrow.